[Release notes] Tampella 5.0.0.73 - Early Access surprisingly brought Android 13 update for X10III in a minor release.
Relnotes warn about needing to uninstall gapps for update. Let us know here how that went for y’all!
EDIT Since opengapps never made it past A11, we’re going to have to force-upgrade probably to MindTheGapps or NikGapps, as described above. Working on upgrading my gist.
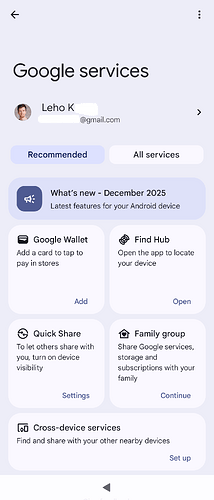
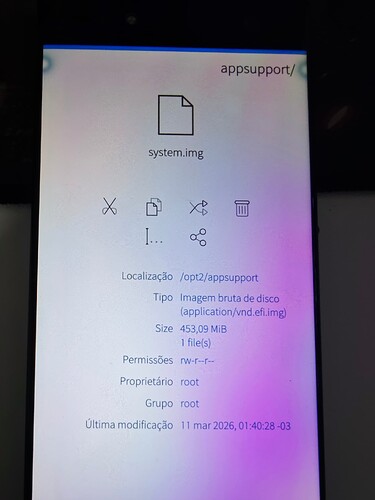
![]() check what OpenGApps injected
check what OpenGApps injected ![]()
$ diff -urN <(unsquashfs -l -dest '' system.img.orig.20250417T225429 | sort) <(unsquashfs -l -dest '' system.img.opengapps | sort)
--- /dev/fd/63 2026-02-07 15:50:11.683124926 +0200
+++ /dev/fd/62 2026-02-07 15:50:11.683124926 +0200
@@ -22,6 +22,7 @@
odm/lib
odm/lib64
oem
+orig_img_path.txt
proc
product
run
@@ -1084,6 +1085,9 @@
system/etc/compatconfig/libcore-platform-compat-config.xml
system/etc/compatconfig/services-platform-compat-config.xml
system/etc/compatconfig/settings-platform-compat-config.xml
+system/etc/default-permissions
+system/etc/default-permissions/default-permissions.xml
+system/etc/default-permissions/opengapps-permissions-q.xml
system/etc/default_volume_tables.xml
system/etc/dirty-image-objects
system/etc/event-log-tags
@@ -1197,12 +1201,18 @@
system/etc/permissions/com.android.settings.xml
system/etc/permissions/com.android.storagemanager.xml
system/etc/permissions/com.android.systemui.xml
+system/etc/permissions/com.google.android.maps.xml
+system/etc/permissions/com.google.android.media.effects.xml
system/etc/permissions/javax.obex.xml
system/etc/permissions/org.apache.http.legacy.xml
system/etc/permissions/platform.xml
+system/etc/permissions/privapp-permissions-google.xml
system/etc/permissions/privapp-permissions-platform.xml
+system/etc/permissions/split-permissions-google.xml
system/etc/ppp
system/etc/ppp/ip-up-vpn
+system/etc/preferred-apps
+system/etc/preferred-apps/google.xml
system/etc/preloaded-classes
system/etc/protolog.conf.json.gz
system/etc/public.libraries.txt
@@ -1375,6 +1385,10 @@
system/etc/selinux/plat_service_contexts
system/etc/sysconfig
system/etc/sysconfig/framework-sysconfig.xml
+system/etc/sysconfig/google_build.xml
+system/etc/sysconfig/google_exclusives_enable.xml
+system/etc/sysconfig/google-hiddenapi-package-whitelist.xml
+system/etc/sysconfig/google.xml
system/etc/sysconfig/hiddenapi-package-whitelist.xml
system/etc/sysconfig/preinstalled-packages-platform.xml
system/etc/task_profiles.json
@@ -1716,6 +1730,8 @@
system/framework/com.android.location.provider.jar
system/framework/com.android.mediadrm.signer.jar
system/framework/com.android.media.remotedisplay.jar
+system/framework/com.google.android.maps.jar
+system/framework/com.google.android.media.effects.jar
system/framework/content.jar
system/framework/dpm.jar
system/framework/ethernet-service.jar
@@ -2854,6 +2870,8 @@
system/priv-app/AlienRemoteKeyboard/oat/arm64
system/priv-app/AlienRemoteKeyboard/oat/arm64/AlienRemoteKeyboard.odex
system/priv-app/AlienRemoteKeyboard/oat/arm64/AlienRemoteKeyboard.vdex
+system/priv-app/AndroidMigratePrebuilt
+system/priv-app/AndroidMigratePrebuilt/AndroidMigratePrebuilt.apk
system/priv-app/BackupRestoreConfirmation
system/priv-app/BackupRestoreConfirmation/BackupRestoreConfirmation.apk
system/priv-app/BackupRestoreConfirmation/oat
@@ -2872,6 +2890,8 @@
system/priv-app/CalendarProvider/oat/arm64
system/priv-app/CalendarProvider/oat/arm64/CalendarProvider.odex
system/priv-app/CalendarProvider/oat/arm64/CalendarProvider.vdex
+system/priv-app/ConfigUpdater
+system/priv-app/ConfigUpdater/ConfigUpdater.apk
system/priv-app/ContactsProvider
system/priv-app/ContactsProvider/ContactsProvider.apk
system/priv-app/ContactsProvider/oat
@@ -2916,6 +2936,12 @@
system/priv-app/FusedLocation/oat/arm64
system/priv-app/FusedLocation/oat/arm64/FusedLocation.odex
system/priv-app/FusedLocation/oat/arm64/FusedLocation.vdex
+system/priv-app/GoogleOneTimeInitializer
+system/priv-app/GoogleOneTimeInitializer/GoogleOneTimeInitializer.apk
+system/priv-app/GoogleRestore
+system/priv-app/GoogleRestore/GoogleRestore.apk
+system/priv-app/GoogleServicesFramework
+system/priv-app/GoogleServicesFramework/GoogleServicesFramework.apk
system/priv-app/InProcessNetworkStack
system/priv-app/InProcessNetworkStack/InProcessNetworkStack.apk
system/priv-app/InProcessNetworkStack/oat
@@ -2952,12 +2978,16 @@
system/priv-app/PackageInstaller/oat/arm64/PackageInstaller.odex
system/priv-app/PackageInstaller/oat/arm64/PackageInstaller.vdex
system/priv-app/PackageInstaller/PackageInstaller.apk
+system/priv-app/Phonesky
+system/priv-app/Phonesky/Phonesky.apk
system/priv-app/PlatformNetworkPermissionConfig
system/priv-app/PlatformNetworkPermissionConfig/oat
system/priv-app/PlatformNetworkPermissionConfig/oat/arm64
system/priv-app/PlatformNetworkPermissionConfig/oat/arm64/PlatformNetworkPermissionConfig.odex
system/priv-app/PlatformNetworkPermissionConfig/oat/arm64/PlatformNetworkPermissionConfig.vdex
system/priv-app/PlatformNetworkPermissionConfig/PlatformNetworkPermissionConfig.apk
+system/priv-app/PrebuiltGmsCore
+system/priv-app/PrebuiltGmsCore/PrebuiltGmsCore.apk
system/priv-app/ProxyHandler
system/priv-app/ProxyHandler/oat
system/priv-app/ProxyHandler/oat/arm64
EDIT Updated script to MTG Sony 10 III - Dual SIM (arm64) | Sailfish OS 5.0.0.73 | Android 13 | MindTheGapps installation script · GitHub using Opus 4.6 and reviewing all changes. MTG archive structure is significantly simpler.
Changes made:
- Replaced OpenGApps with MindTheGapps — Removed lzip-compressed tarball extraction, Fedora RPM installer, browser download polling loop. Replaced with simple unzip ‘system/*’ since MindTheGapps uses a flat
system/ tree. - Pinned filename pattern to MindTheGapps-13.0.0-arm64-*.zip for Android
13. - Fixed all shellcheck violations — Added #!/bin/bash shebang, removed dead $1 parameter from _find_mindthegapps(), added directives for indirect function refs and sourced files.
- Added OS version safety check — Sources /etc/os-release and verifies VERSION_ID=5.0.0.73 before proceeding.
- Cleanup — Removed VelvetTitan (tangorpro-specific), addon.d scripts (irrelevant for Sailfish OS), and obsolete dependencies (lzip).
Result: Script reduced from ~204 to ~148 lines.
![]() WARNING: I haven’t tested it on the phone yet!
WARNING: I haven’t tested it on the phone yet!